[PDF&VCE] Latest 300-209 Dumps PDF Free Download In Lead2pass (141-160)
2016 October Cisco Official New Released 300-209 Dumps in Lead2pass.com! 100% Free Download! 100% Pass Guaranteed! How to 100% pass 300-209 exam? Lead2pass provides the guaranteed 300-209 exam dumps to boost up your confidence in 300-209 exam. Successful candidates have provided their reviews about our 300-209 dumps. Now Lead2pass supplying the new version of 300-209 VCE and PDF dumps. We ensure our 300-209 exam questions are the most complete and authoritative compared with others', which will ensure your 300-209 exam pass. Following questions and answers are all new published by Cisco Official Exam Center: http://www.lead2pass.com/300-209.html 6 1 QUESTION 141
Which technology is FlexVPN based on? A. OER
B. VRF
C. IKEv2
D. an RSA nonce 
Answer: C QUESTION 142
Which application does the Application Access feature of Clientless VPN support? A. TFTP
B. VoIP
C. Telnet
D. active FTP Answer: C QUESTION 143
Where do you configure AnyConnect certificate-based authentication in ASDM? A. group policies
B. AnyConnect Connection Profile
C. AnyConnect Client Profile
D. Advanced Network (Client) Access Answer: B QUESTION 144
Which protocols does the Cisco AnyConnect client use to build multiple connections to the security appliance? A. TLS and DTLS
B. IKEv1
C. L2TP over IPsec
D. SSH over TCP Answer: A QUESTION 145
Which is used by GETVPN, FlexVPN and DMVPN? A. NHRP
B. MPLS
C. GRE
D. ESP Answer: D QUESTION 146
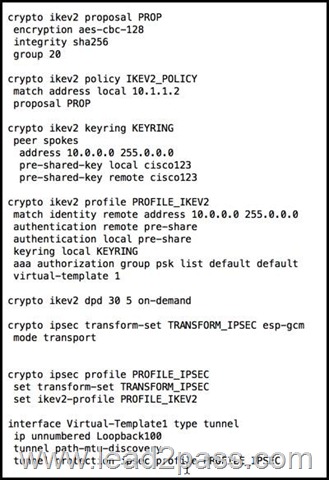
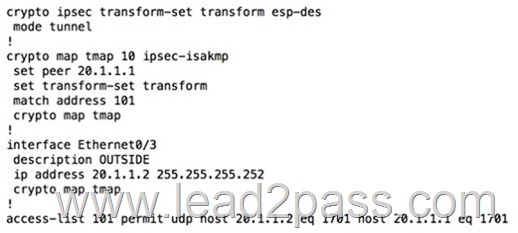
Refer to the exhibit. Which VPN solution does this configuration represent?
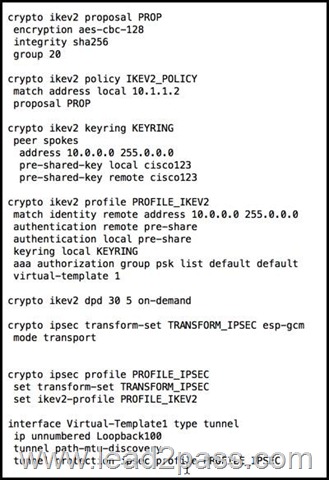 A. DMVPN
B. GETVPN
C. FlexVPN
D. site-to-site Answer: C QUESTION 147
Which VPN solution is best for a collection of branch offices connected by MPLS that frequenty make VoIP calls between branches? A. GETVPN
B. Cisco AnyConnect
C. site-to-site
D. DMVPN Answer: A QUESTION 148
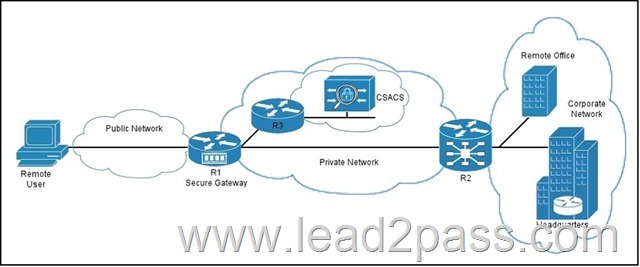
Refer to the exhibit. You have implemented an SSL VPN as shown.
Which type of communication takes place between the secure gateway R1 and the Cisco Secure ACS?
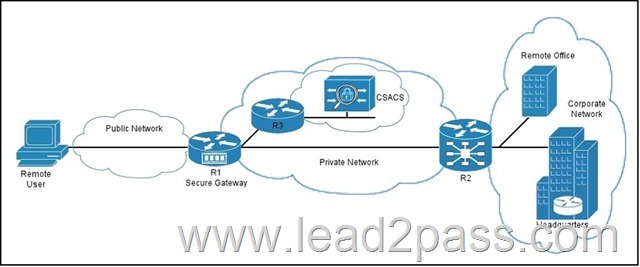 A. HTTP proxy
B. AAA
C. policy
D. port forwarding Answer: B QUESTION 149
Which technology can provide high availability for an SSL VPN? A. DMVPN
B. a multiple-tunnel configuration
C. a Cisco ASA pair in active/passive failover configuration
D. certificate to tunnel group maps Answer: C QUESTION 150
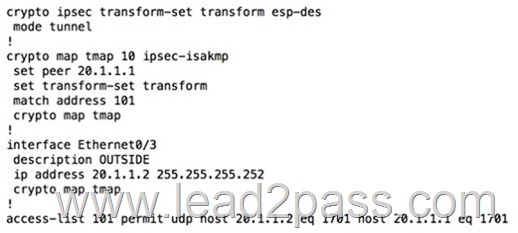
Refer to the exhibit. Which VPN solution does this configuration represent?
 A. Cisco AnyConnect
B. IPsec
C. L2TP
D. SSL VPN Answer: B QUESTION 151
Which technology must be installed on the client computer to enable users to launch applications from a Clientless SSL VPN? A. Java
B. QuickTime plug-in
C. Silverlight
D. Flash Answer: A QUESTION 152
In the Diffie-Hellman protocol, which type of key is the shared secret? A. a symmetric key
B. an asymmetric key
C. a decryption key
D. an encryption key Answer: A QUESTION 153
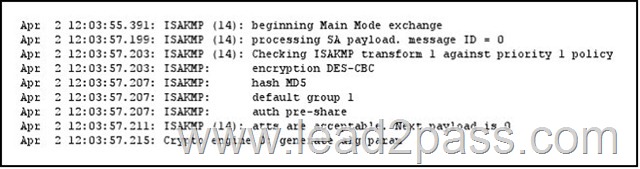
Refer to the exhibit. Which exchange does this debug output represent?
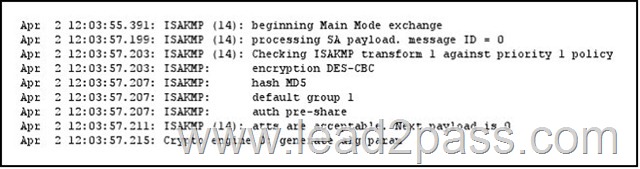 A. IKE Phase 1
B. IKE Phase 2
C. symmetric key exchange
D. certificate exchange Answer: A QUESTION 154
Which two technologies are considered to be Suite B cryptography? (Choose two.) A. MD5
B. SHA2
C. Elliptical Curve Diffie-Hellman
D. 3DES
E. DES Answer: BC QUESTION 155
Which protocol does DTLS use for its transport? A. TCP
B. UDP
C. IMAP
D. DDE Answer: B QUESTION 156
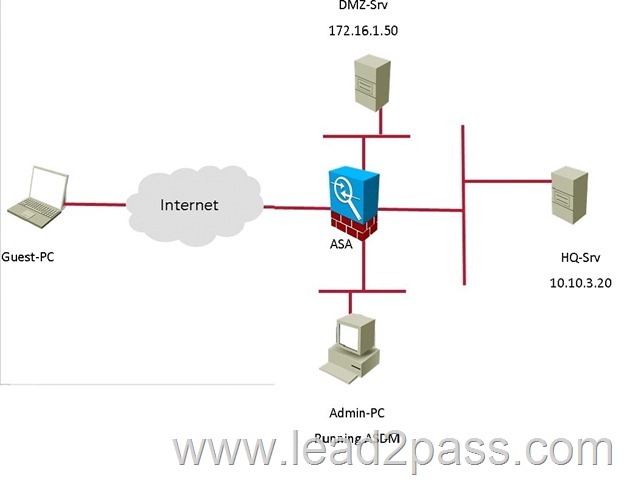
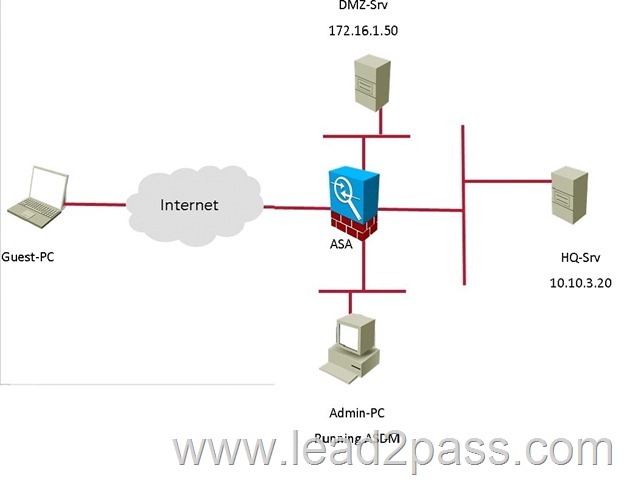
Scenario:
You are the network security manager for your organization.
Your manager has received a request to allow an external user to access to your HQ and DM2 servers.
You are given the following connection parameters for this task.
Using ASDM on the ASA, configure the parameters below and test your configuration by accessing the Guest PC. Not all AS DM screens are active for this exercise.
Also, for this exercise, all changes are automatically applied to the ASA and you will not have to click APPLY to apply the changes manually.
• Enable Clientless SSL VPN on the outside interface
• Using the Guest PC, open an Internet Explorer window and test and verify the basic connection to the SSL VPN portal using address: https://vpn-secure-x.public 2
• a. You may notice a certificate error in the status bar, this can be ignored for this exercise
• b. Username: vpnuser
• c. Password: cisco123
• d. Logout of the portal once you have verified connectivity
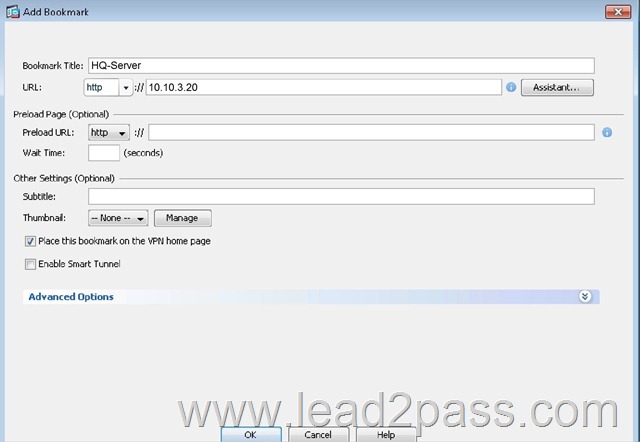
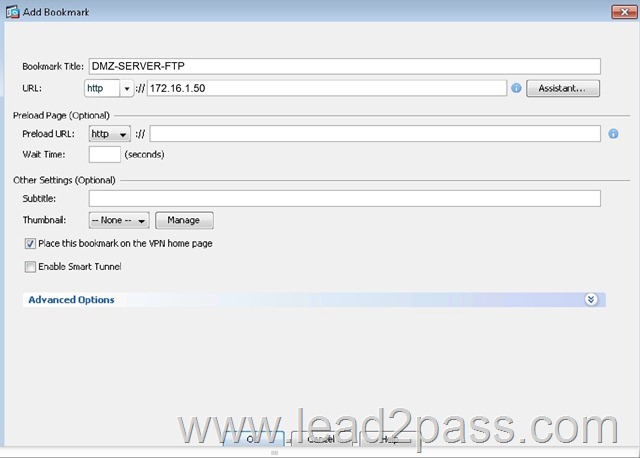
• Configure two bookmarks with the following parameters:
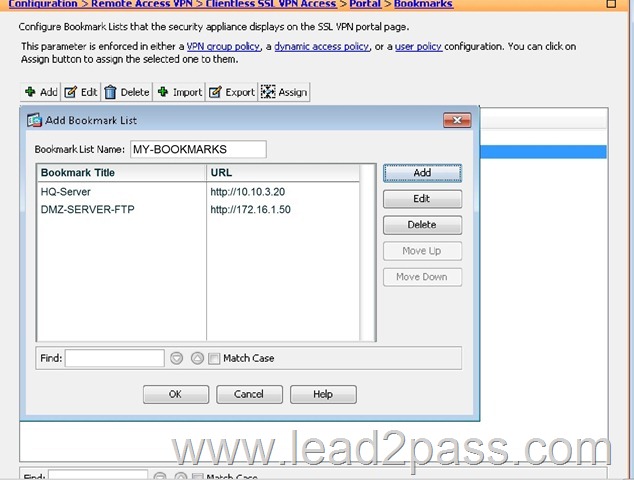
• a. Bookmark List Name: MY-BOOKMARKS
• b. Use the: URL with GET or POST method
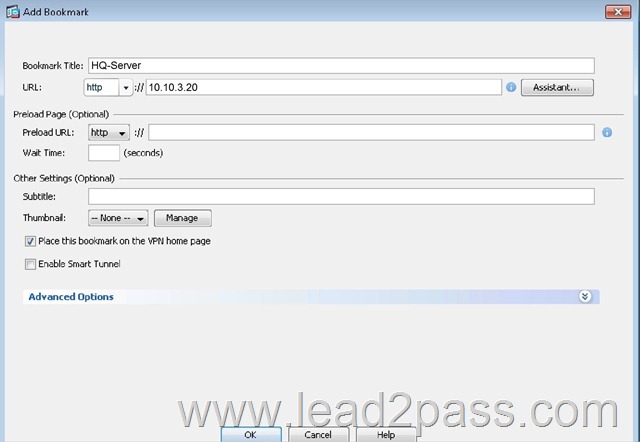
• c. Bookmark Title: HQ-Server
• i. http://10.10.3.20 3
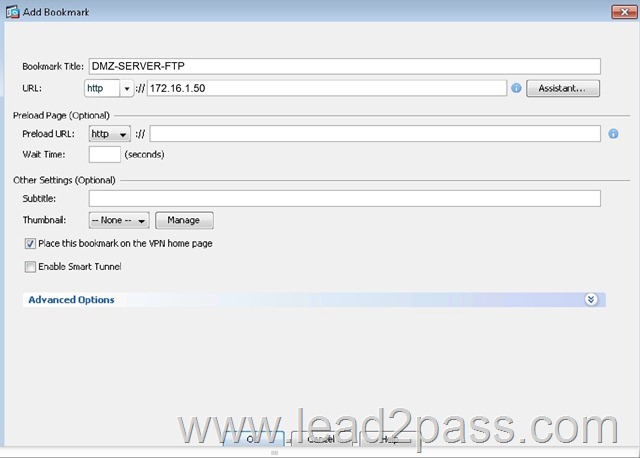
• d. Bookmark Title: DMZ-Server-FTP
• i. ftp://172.16.1.50 4
• e. Assign the configured Bookmarks to:
• i. DfltGrpPolicy
• ii. DfltAccessPolicy
• iii. LOCAL User: vpnuser
• From the Guest PC, reconnect to the SSL VPN Portal
• Test both configured Bookmarks to ensure desired connectivity
You have completed this exercise when you have configured and successfully tested Clientless SSL VPN connectivity.
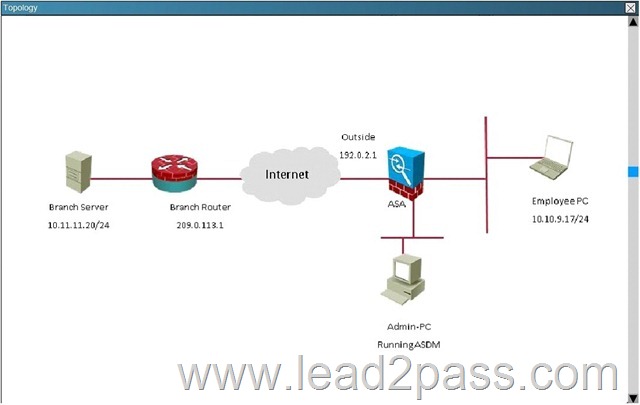
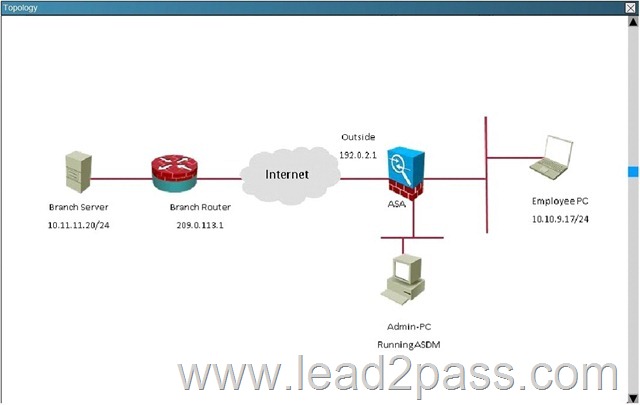
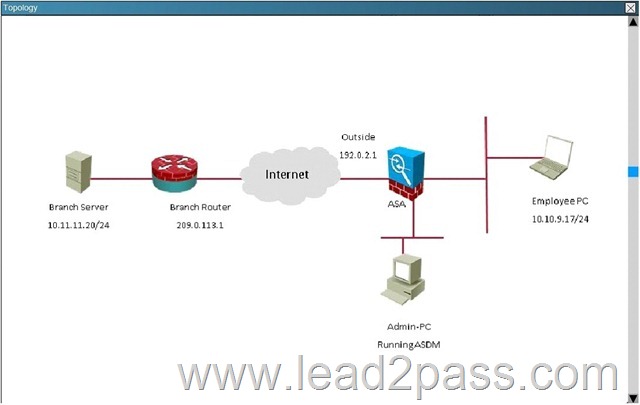
Topology:
Answer:
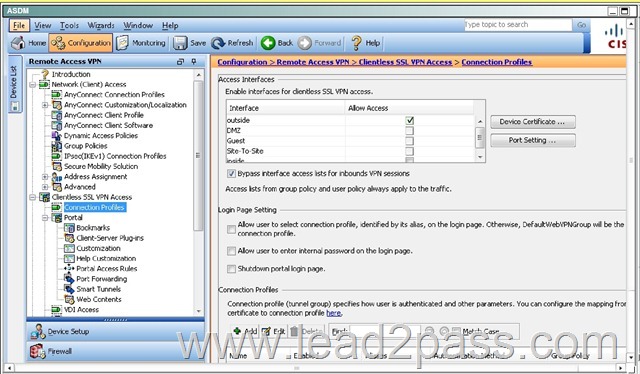
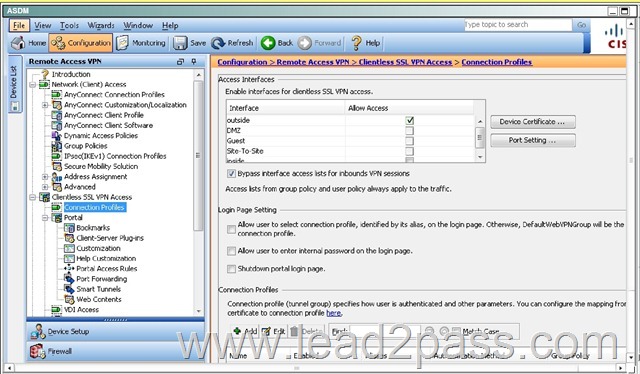
First, enable clientless VPN access on the outside interface by checking the box found below:
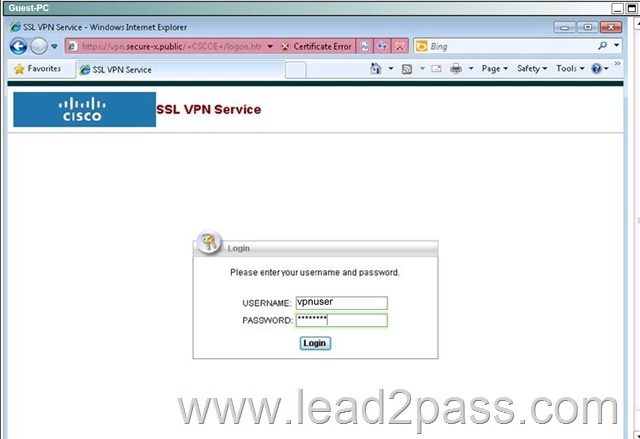
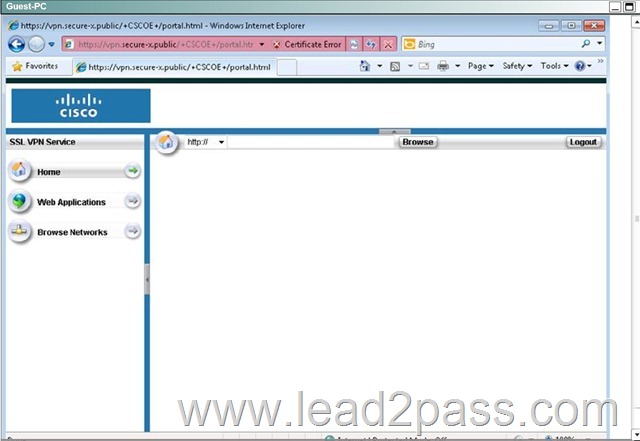
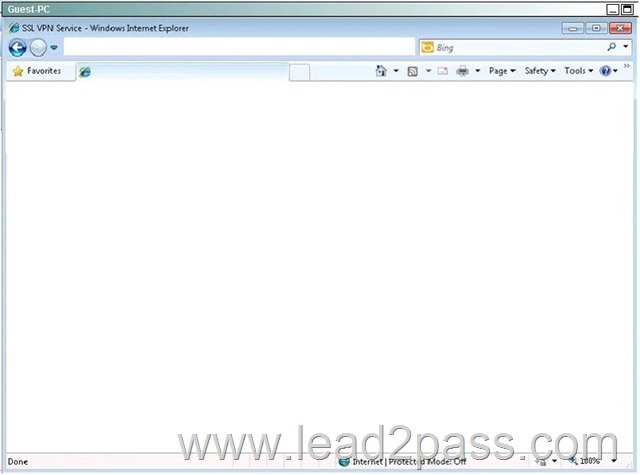
Then, log in to the given URL using the vpnuser/cisco123 credentials:
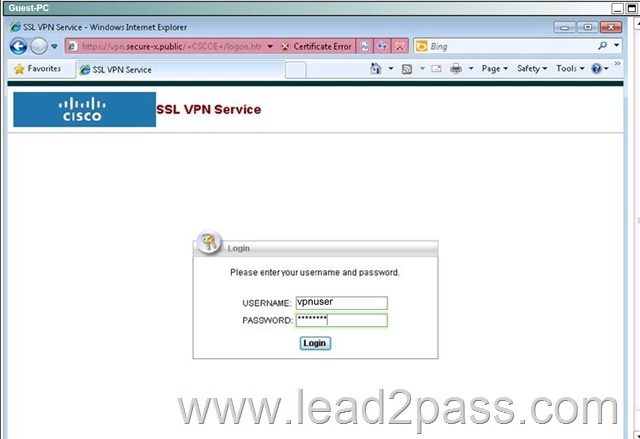
Logging in will take you to this page, which means you have now verified basic connectivity:
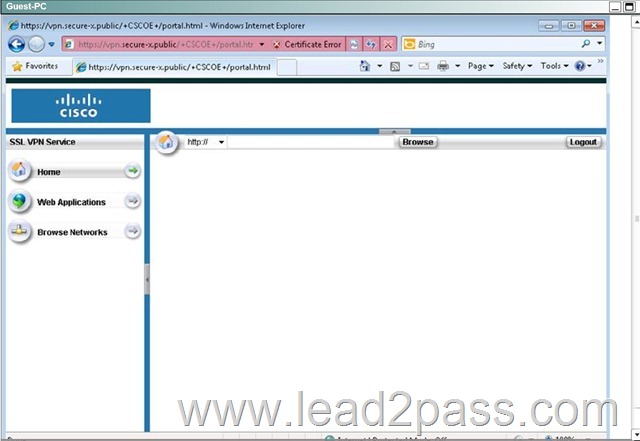
Now log out by hitting the logout button.
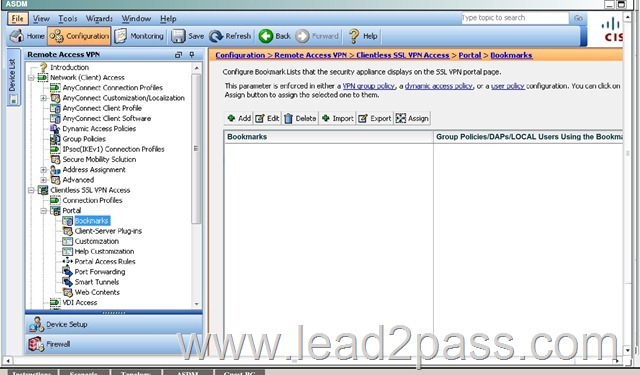
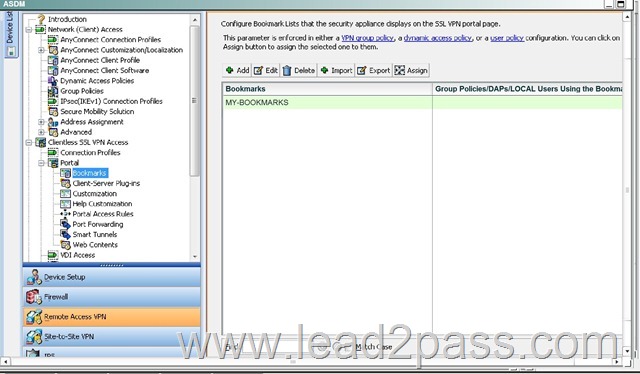
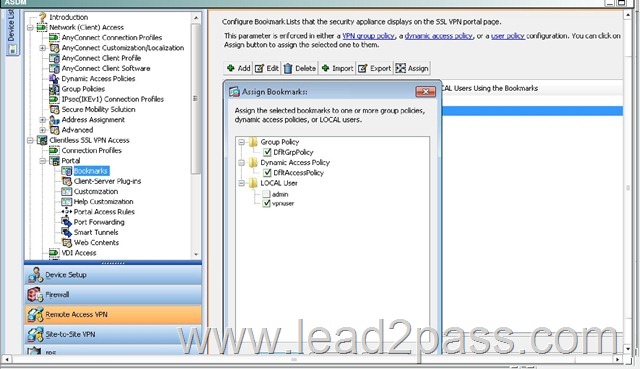
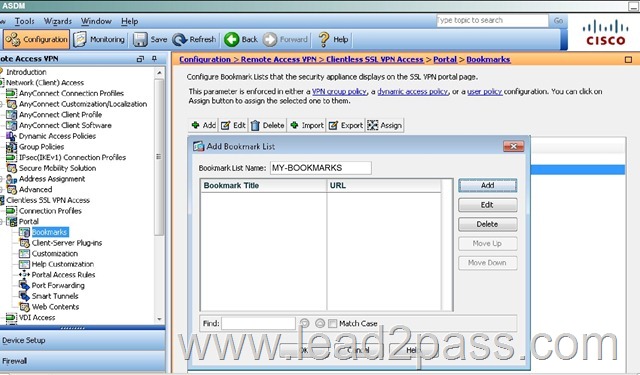
Now, go back to the ASDM and navigate to the Bookmarks portion:
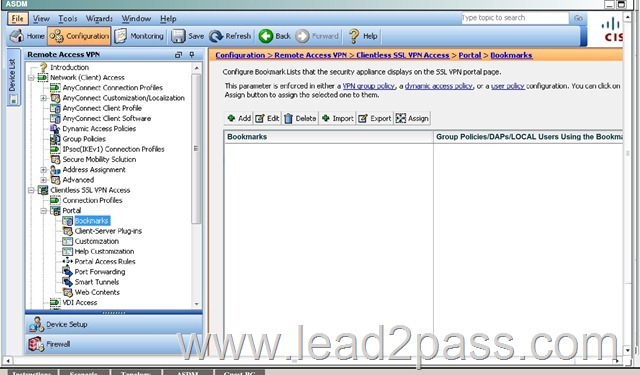
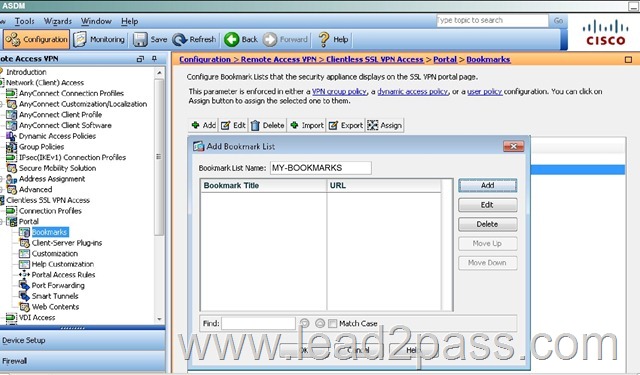
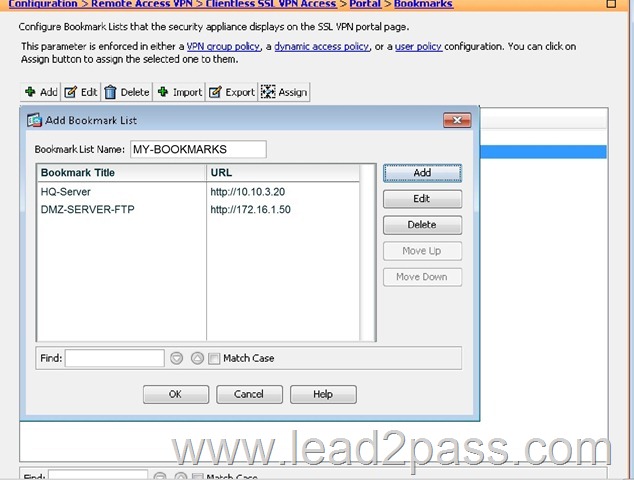
Make the name MY-BOOKMARKS and use the “Add” tab and add the bookmarks per the instructions:
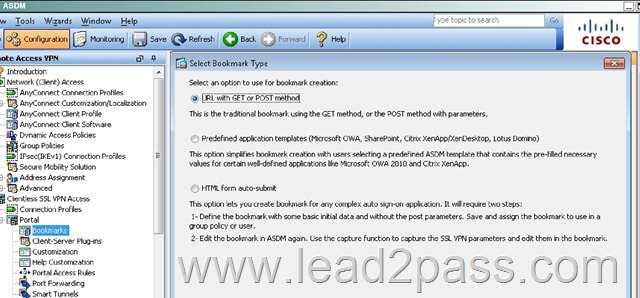
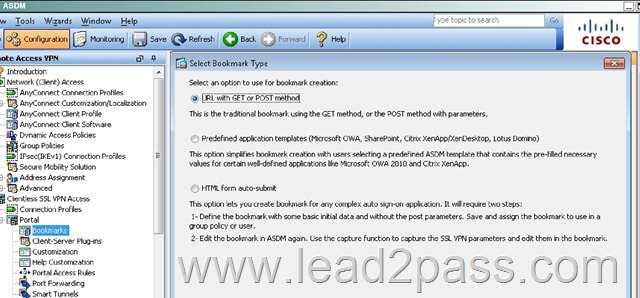
Ensure the “URL with GET of POST method” button is selected and hit OK:
Add the two bookmarks as given in the instructions:
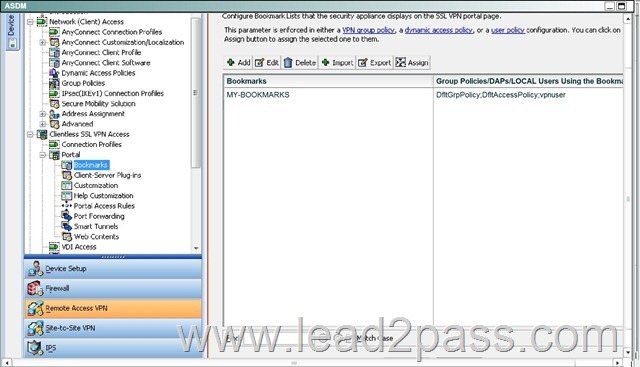
Hit OK and you will see this:
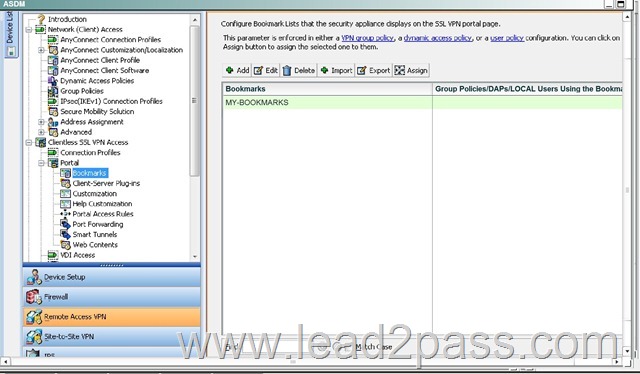
Select the MY-BOOKMARKS Bookmarks and click on the “Assign” button.
Then, click on the appropriate check boxes as specified in the instructions and hit OK.
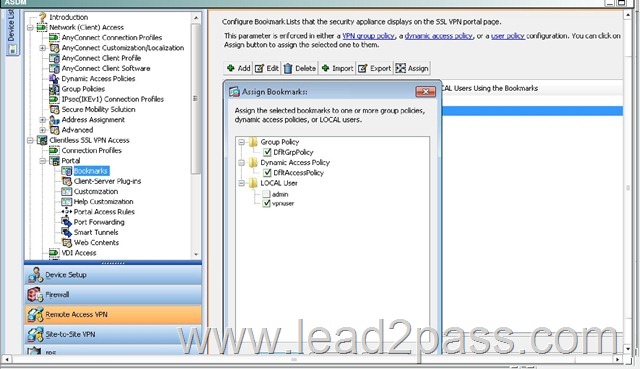
After hitting OK, you will now see this:
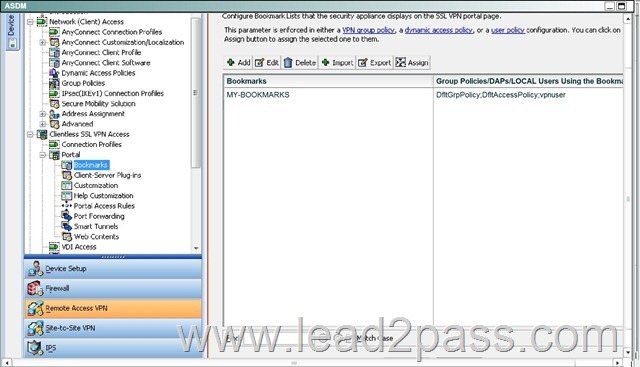
Then, go back to the Guest-PC, log back in and you should be able to test out the two new bookmarks. QUESTION 157
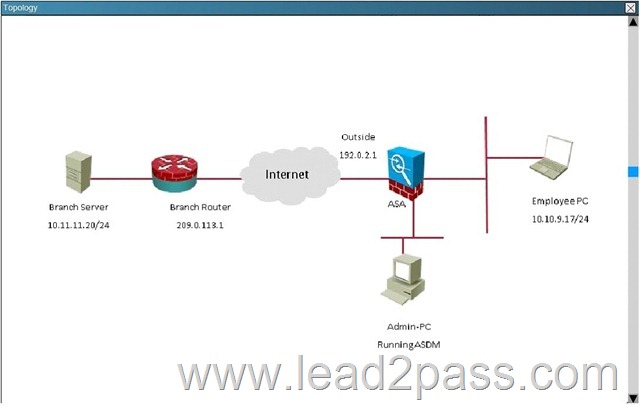
Scenario:
You are the senior network security administrator for your organization. Recently and junior engineer configured a site-to-site IPsec VPN connection between your headquarters Cisco ASA and a remote branch office.
You are now tasked with verifying the IKEvl IPsec installation to ensure it was properly configured according to designated parameters. Using the CLI on both the Cisco ASA and branch ISR. verify the IPsec configuration is properly configured between the two sites.
NOTE: the show running-config command cannot be used for the this exercise.
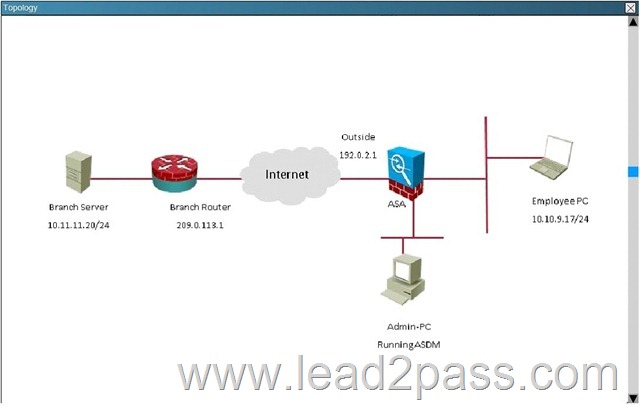
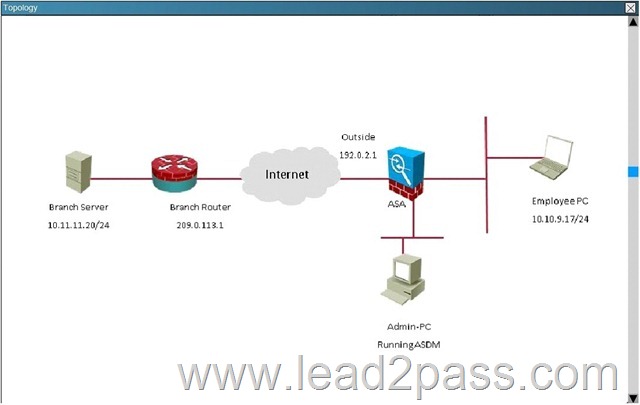
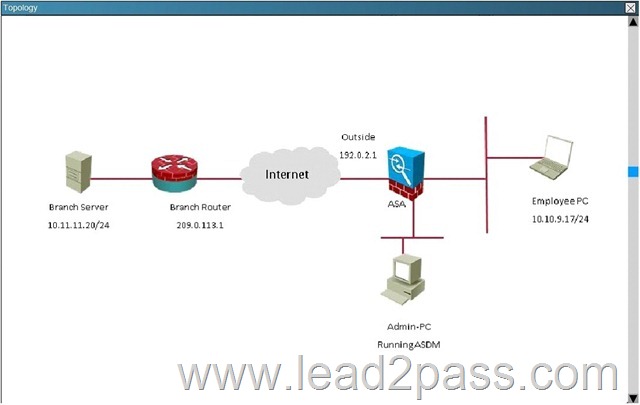
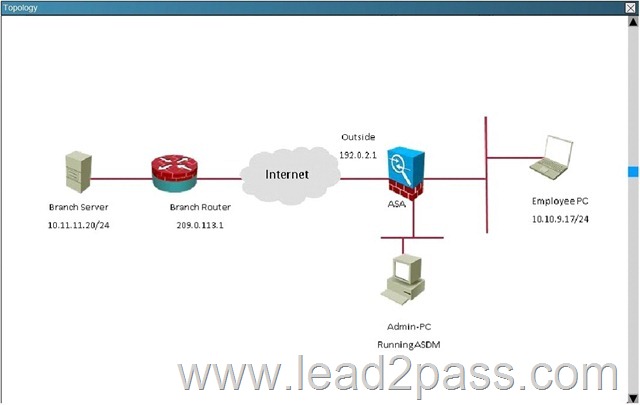
Topology:
What is being used as the authentication method on the branch ISR? A. Certifcates
B. Pre-shared keys
C. RSA public keys
D. Diffie-Hellman Group 2 Answer: B
Explanation:
The show crypto isakmp key command shows the preshared key of "cisco" QUESTION 158
Scenario:
You are the senior network security administrator for your organization. Recently and junior engineer configured a site-to-site IPsec VPN connection between your headquarters Cisco ASA and a remote branch office.
You are now tasked with verifying the IKEvl IPsec installation to ensure it was properly configured according to designated parameters. Using the CLI on both the Cisco ASA and branch ISR. verify the IPsec configuration is properly configured between the two sites.
NOTE: the show running-config command cannot be used for the this exercise.
Topology:
Which transform set is being used on the branch ISR? A. Default
B. ESP-3DES ESP-SHA-HMAC
C. ESP-AES-256-MD5-TRANS mode transport
D. TSET Answer: B
Explanation:
This can be seen from the "show crypto ipsec sa" command as shown below: QUESTION 159
Scenario:
You are the senior network security administrator for your organization. Recently and junior engineer configured a site-to-site IPsec VPN connection between your headquarters Cisco
ASA and a remote branch office.
You are now tasked with verifying the IKEvl IPsec installation to ensure it was properly configured according to designated parameters. Using the CLI on both the Cisco ASA and branch ISR. verify the IPsec configuration is properly configured between the two sites.
NOTE: the show running-config command cannot be used for the this exercise.
Topology:
In what state is the IKE security association in on the Cisco ASA? A. There are no security associations in place
B. MM_ACTIVE
C. ACTIVE(ACTIVE)
D. QM_IDLE Answer: B
Explanation:
This can be seen from the "show crypto isa sa" command: QUESTION 160
Scenario:
You are the senior network security administrator for your organization. Recently and junior engineer configured a site-to-site IPsec VPN connection between your headquarters Cisco ASA and a remote branch office.
You are now tasked with verifying the IKEvl IPsec installation to ensure it was properly configured according to designated parameters. Using the CLI on both the Cisco ASA and branch ISR. verify the IPsec configuration is properly configured between the two sites.
NOTE: the show running-config command cannot be used for the this exercise.
Topology:
Which crypto map tag is being used on the Cisco ASA? A. outside_cryptomap
B. VPN-to-ASA
C. L2L_Tunnel
D. outside_map1 Answer: D
Explanation:
This is seen from the "show crypto ipsec sa" command on the ASA. All the 300-209 braindumps are updated. Get a complete hold of 300-209 PDF dumps and 300-209 practice test with free VCE player through Lead2pass and boost up your skills. 300-209 new questions on Google Drive: https://drive.google.com/open?id=0B3Syig5i8gpDODI1TDlUT1lBV00 5 2016 Cisco 300-209 exam dumps (All 237 Q&As) from Lead2pass: http://www.lead2pass.com/300-209.html 6 1 [100% Exam Pass Guaranteed]
|