Free Sharing Of Updated 70-697 VCE And PDF Dumps From Lead2pass:
https://www.lead2pass.com/70-697.html
QUESTION 21
Hotspot Question
You have an image of Windows 10 Enterprise named Image1. Image1 has version number 1.0.0.0 of a custom, line-of-business universal app named App1.
You deploy Image1 to Computer1 for a user named User1.
You need to update App1 to version 1.0.0.1 on Computer1 for User1 only.
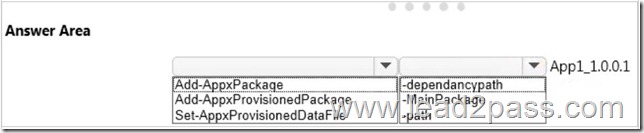
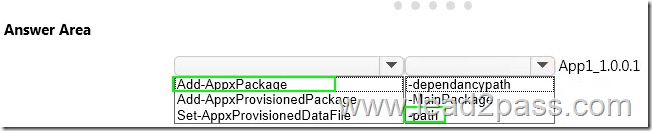
What command should you run? To answer, select the appropriate options in the answer area.
Answer:
Explanation:
In this question, we need to update App1 to version 1.0.0.1 on Computer1 “for User1 only”. The Add-AppxPackage cmdlet adds a signed app package (.appx) to a user account. To update the application, we need to use the -path parameter to specify the path to the upgraded application.
Incorrect Answers:
add-provisionedappxpackage would make the app available to all users, not just User1 only. Set-AppXProvisionedDataFile adds custom data into an app. It does not update it to a later version.
https://technet.microsoft.com/en-us/library/hh856048.aspx
http://blogs.technet.com/b/sunshine/archive/2014/03/22/updating-a-modern-app-in-windows-8.aspx
QUESTION 22
Drag and Drop Question
You manage Microsoft Intune for a company named Contoso.
You have an administrative computer named Computer1 that runs Windows 10 Enterprise.
You need to add a Windows Store universal app named App1 to the Company Portal Apps list for all users.
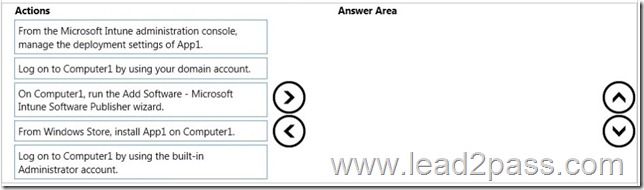
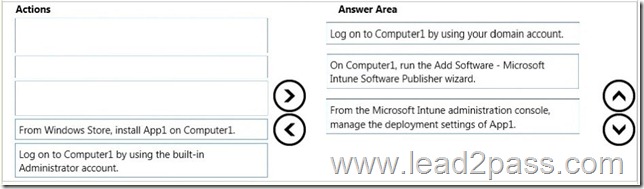
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Answer:
Explanation:
1. Log into your computer using a domain account.
2. Run the Microsoft Intune Software Publisher wizard app.
3. Configure the deployment settings of the app.
Incorrect Answers:
You do not need to install App1 on Computer1.
You need to log in with a domain account, not a local administrator account.
https://technet.microsoft.com/en-gb/library/dn646961.aspx
https://technet.microsoft.com/en-gb/library/dn646955.aspx#BKMK_SoftwareDistProcess
QUESTION 23
Your network contains an Active Directory domain named contoso.com.
The domain contains Windows 10 Enterprise client computers.
Your company has a subscription to Microsoft Office 365. Each user has a mailbox that is stored in Office 365 and a user account in the contoso.com domain. Each mailbox has two email addresses.
You need to add a third email address for each user.
What should you do?
A. From Active Directory Users and Computers, modify the E-mail attribute for each user.
B. From Microsoft Azure Active Directory Module for Windows PowerShell, run the Set-Mailbox cmdlet.
C. From Active Directory Domains and Trust, add a UPN suffix for each user.
D. From the Office 365 portal, modify the Users settings of each user.
Answer: B
Explanation:
We can use the Set-Mailbox cmdlet to modify the settings of existing mailboxes.
The EmailAddresses parameter specifies all the email addresses (proxy addresses) for the recipient, including the primary SMTP address. In on-premises Exchange organizations, the primary SMTP address and other proxy addresses are typically set by email address policies. However, you can use this parameter to configure other proxy addresses for the recipient.
To add or remove specify proxy addresses without affecting other existing values, use the following syntax:
@{Add=”[<Type>]:<emailaddress1>”,”[<Type>]:<emailaddress2>”…; Remove=”[<Type>]:<emailaddress2>”,”[<Type>]:<emailaddress2>”…}.
Incorrect Answers:
A: You cannot use the E-mail attribute in Active Directory Users and Computers to add email addresses.
C: A UPN (User Principal Name) is used for authentication when you enter your credentials as [email protected] instead of: domainname\username. A UPN suffix is not an email address.
D: Users’ email addresses are not configured in the User settings in the Office 365 portal.
https://technet.microsoft.com/en-us/library/bb123981(v=exchg.160).aspx
QUESTION 24
Hotspot Question
You manage a Microsoft Azure RemoteApp deployment. The deployment consists of a cloud collection named CloudCollection1 and a hybrid collection named HybridCollection1. Both collections reside in a subscription named Subscription1. Subscription1 contains two Active Directory instances named AzureAD1 and AzureAD2. AzureAD1 is the associated directory of Subcsription1.
AzureAD1 is synchronized to an on-premises Active Directory forest named constoso.com. Passwords are synchronized between AzureAD1 and the on-premises Active Directory.
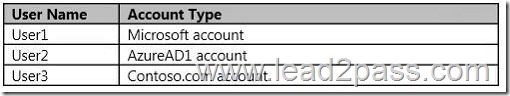
You have the following user accounts:
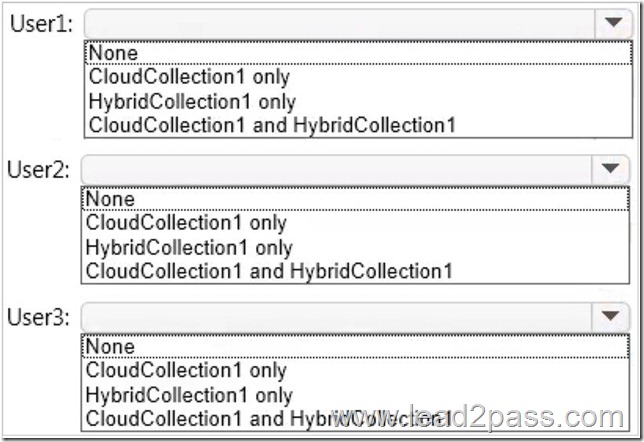
You need to identify to which collections each user can be assigned access.
What should you identify? To answer, select the appropriate options in the answer area.
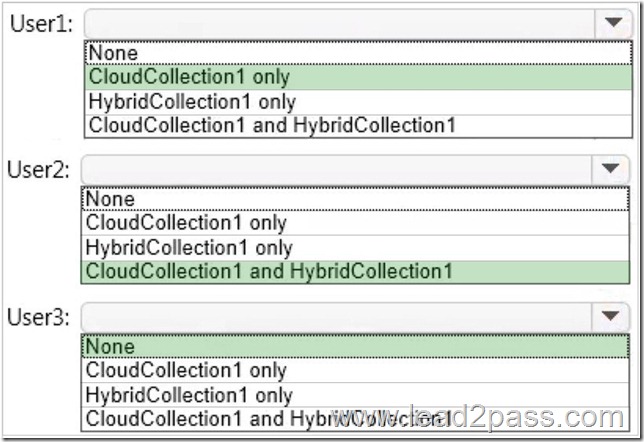
Answer:
Explanation:
A Microsoft account can only access a cloud collection.
An Azure Active Directory (Azure AD) account can access a cloud collection and it can access a hybrid collection if directory synchronization with password sync is deployed. An on-premise domain account that does not exist in any Azure Active Directory cannot access Azure cloud resources.
https://azure.microsoft.com/en-gb/documentation/articles/remoteapp-collections/
QUESTION 25
Your Windows 10 Enterprise work computer is a member of an Active Directory domain.
You use your domain account to log on to the computer.
You use your Microsoft account to log on to a home laptop.
You want to access Windows 10 Enterprise apps from your work computer by using your Microsoft account.
You need to ensure that you are able to access the Windows 10 Enterprise apps on your work computer by logging on only once.
What should you do?
A. Add the Microsoft account as a user on your work computer.
B. Enable Remote Assistance on your home laptop.
C. Connect your Microsoft account to your domain account on your work computer.
D. Install SkyDrive for Windows on both your home laptop and your work computer.
Answer: C
Explanation:
You can connect your Microsoft account to your domain account on your work computer. This will enable you to sign in to your work computer with your Microsoft account and access the same resources that you would access if you were logged in with your domain account.
When you connect your Microsoft account to your domain account, you can sync your settings and preferences between them. For example, if you use a domain account in the workplace, you can connect your Microsoft account to it and see the same desktop background, app settings, browser history and favorites, and other Microsoft account settings that you see on your home PC.
Incorrect Answers:
A: If you add the Microsoft account as a user on your work computer, this would be a separate account with no domain access. The account would not have access to the resources that you access with your domain account.
B: Enabling Remote Assistance on your home laptop would just enable you to send remote assistance invitations from your home laptop. It would have no effect on your work computer or your ability to log on to it.
D: SkyDrive is a cloud storage solution. You can save your files on SkyDrive and access them from any device. Installing SkyDrive will not enable you to log on to your work computer with your Microsoft account.
http://windows.microsoft.com/en-gb/windows-8/connect-microsoft-domain-account
QUESTION 26
You have a Windows 10 Enterprise computer named Computer1 that has the Hyper-V feature installed. Computer1 hosts a virtual machine named VM1. VM1 runs Windows 10 Enterprise. VM1 connects to a private virtual network switch.
From Computer1, you need to remotely execute Windows PowerShell cmdlets on VM1.
What should you do?
A. Run the winrm.exe command and specify the -s parameter.
B. Run the Powershell.exe command and specify the -Command parameter.
C. Run the Receive-PSSession cmdlet and specify the -Name parameter.
D. Run the Invoke-Command cmdlet and specify the -VMName parameter.
Answer: D
Explanation:
We can use Windows PowerShell Direct to run PowerShell cmdlets on a virtual machine from the Hyper-V host. Because Windows PowerShell Direct runs between the host and virtual machine, there is no need for a network connection or to enable remote management.
There are no network or firewall requirements or special configuration. It works regardless of your remote management configuration. To use it, you must run Windows 10 or Windows Server Technical Preview on the host and the virtual machine guest operating system.
To create a PowerShell Direct session, use one of the following commands:
Enter-PSSession -VMName VMName
Invoke-Command -VMName VMName -ScriptBlock { commands }
Incorrect Answers:
A: WinRM is Windows Remote Management. This is not required when using Windows PowerShell Direct.
B: Running PowerShell.exe with a PowerShell cmdlet will execute the PowerShell cmdlet on the local machine. It will not remotely execute the PowerShell cmdlet on the VM.
C: You could run the Enter-PSSession cmdlet with the -VMName parameter but the Receive-PSSession cmdlet with the 璑ame parameter will not work.
https://msdn.microsoft.com/en-us/virtualization/hyperv_on_windows/about/whats_new
QUESTION 27
You deploy several tablet PCs that run Windows 10 Enterprise.
You need to minimize power usage when the user presses the sleep button.
What should you do?
A. In Power Options, configure the sleep button setting to Sleep.
B. In Power Options, configure the sleep button setting to Hibernate.
C. Configure the active power plan to set the system cooling policy to passive.
D. Disable the C-State control in the computer’s BIOS.
Answer: B
Explanation:
We can minimize power usage on the tablet PCs by configuring them to use Hibernation mode.
A computer in hibernation mode uses no power at all.
Hibernation is a power-saving state designed primarily for laptops. While sleep puts your work and settings in memory and draws a small amount of power, hibernation puts your open documents and programs on your hard disk, and then turns off your computer. Of all the power-saving states in Windows, hibernation uses the least amount of power. On a laptop, use hibernation when you know that you won’t use your laptop for an extended period and won’t have an opportunity to charge the battery during that time.
Incorrect Answers:
A: Sleep is a power-saving state that allows a computer to quickly resume full-power operation.
A sleeping computer draws a small amount of power whereas a hibernating computer uses no power.
C: A passive cooling policy slows down the processor before speeding up the processor’s cooling fan to conserve power. However, this will still use more power than a hibernating tablet.
D: C-States are different modes of CPU clock speed used to conserve power when processors are idle.
Disabling C-State control disables the ability to reduce the power consumption of the computer.
http://windows.microsoft.com/en-gb/windows7/sleep-and-hibernation-frequently-asked-questions
QUESTION 28
You are the desktop administrator for a small company.
Your workgroup environment consists of Windows 10 Enterprise computers.
You want to prevent 10 help desk computers from sleeping. However, you want the screens to shut off after a certain period of time if the computers are not being used.
You need to configure and apply a standard power configuration scheme for the 10 help desk computers on your network.
Which two actions should you perform? Each correct answer presents part of the solution.
A. Import the power scheme by using POWERCFG /IMPORT on each of the remaining help desk computers. Set the power scheme to Active by using POWERCFG /S.
B. Use POWERCFG /X on one help desk computer to modify the power scheme to meet the requirements.
Export the power scheme by using POWERCFG /EXPORT.
C. Use POWERCFG /S on one help desk computer to modify the power scheme to meet the requirements.
Export the power scheme by using POWERCFG /EXPORT.
D. Import the power scheme by using POWERCFG /IMPORT on each of the remaining help desk computers. Set the power scheme to Active by using POWERCFG /X.
Answer: AB
Explanation:
You can use the Powercfg.exe tool to control power settings and configure computers to default to Hibernate or Standby modes.
In this question, we use POWERCFG /X on one help desk computer to modify the power scheme to meet our requirements. After configuring the required settings, we can export the power scheme settings to a file by using POWERCFG /EXPORT.
We can then import the power scheme from the file on each of the remaining help desk computers by using POWERCFG /IMPORT. After importing the power scheme on the remaining computers, we need to set the new power scheme to be the active power scheme by using POWERCFG /S.
Incorrect Answers:
C: You need to use the /X switch to modify the power scheme, not the /S switch.
D: You need to use the /S switch to set the power scheme as active, not the /X switch.
https://technet.microsoft.com/en-us/library/cc748940(v=ws.10).aspx
QUESTION 29
A company has an Active Directory Domain Services (AD DS) domain. All client computers run Windows 10 Enterprise. Some computers have a Trusted Platform Module (TPM) chip.
You need to configure a single Group Policy object (GPO) that will allow Windows BitLocker Drive Encryption on all client computers.
Which two actions should you perform? Each correct answer presents part of the solution.
A. Enable the Require additional authentication at startup policy setting.
B. Enable the Enforce drive encryption type on operating system drives policy setting.
C. Enable the option to allow BitLocker without a compatible TPM.
D. Configure the TPM validation profile to enable Platform Configuration Register indices (PCRs) 0, 2, 4, and 11.
Answer: AC
Explanation:
We need to allow Windows BitLocker Drive Encryption on all client computers (including client computers that do not have Trusted Platform Module (TPM) chip).
We can do this by enabling the option to allow BitLocker without a compatible TPM in the group policy. The `Allow BitLocker without a compatible TPM’ option is a checkbox in the `Require additional authentication at startup’ group policy setting. To access the `Allow BitLocker without a compatible TPM’ checkbox, you need to first select Enabled on the `Require additional authentication at startup’ policy setting.
Incorrect Answers:
B: Enabling the `Enforce drive encryption type on operating system drives’ policy setting allows you to configure whether the entire drive or used space only is encrypted when BitLocker is enabled. However, it does not enable the use of BitLocker on computers without a TPM chip.
D: The Platform Configuration Register indices (PCRs) 0, 2, 4, and 11 are enabled by default for computers that use an Extensible Firmware Interface (EFI). Configuring the TPM validation profile does not enable the use of BitLocker on computers without a TPM chip.
http://www.howtogeek.com/howto/6229/how-to-use-bitlocker-on-drives-without-tpm/
QUESTION 30
Employees are permitted to bring personally owned portable Windows 10 Enterprise computers to the office. They are permitted to install corporate applications by using the management infrastructure agent and access corporate email by using the Mail app.
An employee’s personally owned portable computer is stolen.
You need to protect the corporate applications and email messages on the computer.
Which two actions should you perform? Each correct answer presents part of the solution.
A. Prevent the computer from connecting to the corporate wireless network.
B. Change the user’s password.
C. Disconnect the computer from the management infrastructure.
D. Initiate a remote wipe.
Answer: BD
Explanation:
The personally owned portable Windows 10 Enterprise computers being managed by the management infrastructure agent enables the use of remote wipe. By initiating a remote wipe, we can erase all company data including email from the stolen device.
Microsoft Intune provides selective wipe, full wipe, remote lock, and passcode reset capabilities. Because mobile devices can store sensitive corporate data and provide access to many corporate resources, you can issue a remote device wipe command from the Microsoft Intune administrator console to wipe a lost or stolen device.
Changing the user’s password should be the first step. If the stolen computer is accessed before the remote wipe happens, the malicious user could be able to access company resources if the laptop has saved passwords.
Incorrect Answers:
A: Preventing the computer from connecting to the corporate wireless network will not offer much protection. The person in possession of the laptop would still be able to access all the data on the laptop and download emails. Furthermore, it is likely that the corporate applications can access corporate servers over any Internet connection.
C: Disconnecting the computer from the management infrastructure will not help. The person in possession of the laptop would still be able to access all the data on the laptop and download emails. This step would also remove the ability to perform a remote wipe. The computer will be disconnected from the management infrastructure when the remote wipe happens.
https://technet.microsoft.com/en-gb/library/jj676679.aspx
70-697 dumps full version (PDF&VCE): https://www.lead2pass.com/70-697.html
Large amount of free 70-697 exam questions on Google Drive: https://drive.google.com/open?id=0B3Syig5i8gpDX3RYMG04cEg5aEE
You may also need:
70-698 exam dumps: https://drive.google.com/open?id=0B3Syig5i8gpDa2cwaDdKY1dLdHM